What new developments have been made in the world of security? What bold innovations are being implemented in a field that warrants such aggressive attention and constant evolution, and what trends are leading the way in terms of technology, usability, expandability and functionality?
After all, as the great thinker and innovator da Vinci famously said: “Iron rusts from disuse; water loses its purity from stagnation…even so does inaction sap the vigour of the mind”.
This is an utterly apropos statement considering that security, when employed to its full potential, should be a mercurial force that is able to adapt to the times. Security as concept should be a shape-shifter, rearranging its various elements and changing its guise to best suit the socio-economic climate.
Think about it.
Five hundred years ago the biggest threat was that your castle would be attacked by the neighbouring kingdom (that is, of course, assuming that you were a member of nobility) and the need arose for some means of fortification. While weapons such as trebuchets and catapults could pack quite a wallop even from a distance, particular attention was given to securing the entrances and thus drawbridges, portcullises and barbicans became the norm.
Today, intruders do not announce themselves with trumpets, war drums and battle cries – indeed, you only become aware that they have paid you an unsolicited visit once you arrive home to find your belongings gone. The modern criminal has undoubtedly become wilier, more resourceful, and as such one would like to believe that security has similarly evolved to catch the proverbial curveballs these evildoers like to throw at us.
So what has been making waves in this arena?
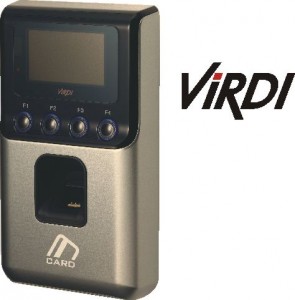
The popularity of biometric authentication has certainly been on the increase, with futuristic-looking fingerprint readers gracing the entrances of many a high-security establishment. Indeed, in a marvellous display of forward thinking, certain banks have started implementing fingerprint identification in the entrance airlocks, requiring patrons to scan a thumb before being granted access. This is a brilliant innovation since it allows banks to have the fingerprints of those entering the premises on record should things go awry, effectively putting them one step ahead of criminals. The advent of biometrics is perhaps a sign that we are slowly transitioning out of an age in which we were separated from technology by virtue of biology, and into an era where our own DNA has become the access card. It was an inevitable – and necessary – change, and one which is lauded for its dependability and efficiency by those in the know. After all, DNA is something that – thus far, at least – is completely unique to the individual. What can be more secure than that?
Enter GSM technology.
Ever since mobile phones became a natural extension of our arms, industry players have been looking for ways in which to bring security to the cell-front. This breakthrough came with the advent of GSM-modules – intelligent devices that can be used for the activation of any number of electrical devices, and can also be configured to provide text message notifications when the unit’s inputs are activated. The security benefits of this innovation are phenomenal. As an example of this, imagine being able to arm the alarm of your house in Cape Town while you’re vacationing in Rome; or receiving a SMS notification that someone is tampering with your gate’s infrared safety beams. GSM technology has made this possible.

If you are among those concerned that access automation has been stagnating for the last decade or so, you’ll be relieved to know that some remarkable advances have been made in this arena, with everything from integrated timer technology to pedestrian access control forming part of the list of available solutions.
But let’s take a moment to discuss the abovementioned timer technology, lest the importance and usefulness of it be ignored.
Imagine, if you will, that you are the owner of an engineering firm the employees of which have all been issued with remote controls. At first glance this seems like a convenient access solution that leaves very little room for error. However, this means that workers now have access to the premises not only during working hours, but whenever it suits them. As you can well imagine, this leaves the system vulnerable and open to abuse. Timer functionality, and the feature known as “time-barring” in particular, addresses this security concern by allowing the user to inhibit certain inputs during pre-configured time periods. In laymen’s terms what this means is that you can set up the system so that the remotes given to staff will only operate during working hours, and will be inhibited during weekends and after work.
The field of security is, at the very least, one that is brimming with possibility. As much as criminals would like to believe that they are in the lead, the hi-tech innovations discussed above as well as countless others not mentioned in this article seem to indicate the contrary. We are in the midst of an exciting transformation, a security renaissance as it were, that could see us enter a whole new age; one in which biology might just come into play as the ultimate access control device, as evidenced by the rising popularity of biometrics.






